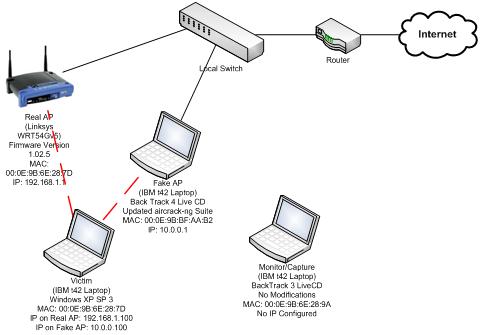
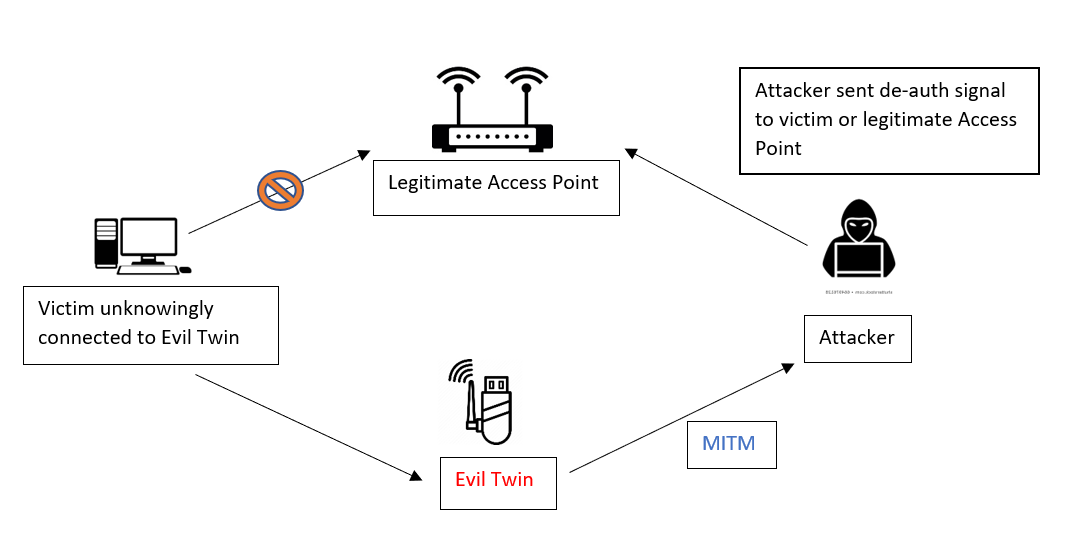
A passive user‐side solution for evil twin access point detection at public hotspots - Hsu - 2020 - International Journal of Communication Systems - Wiley Online Library

A passive user‐side solution for evil twin access point detection at public hotspots - Hsu - 2020 - International Journal of Communication Systems - Wiley Online Library
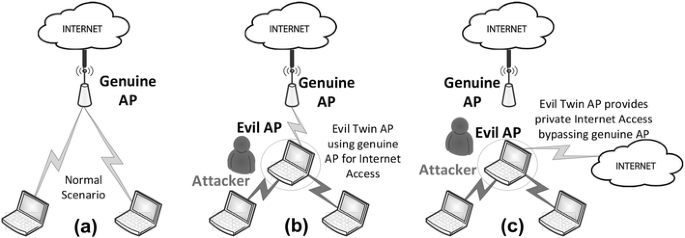
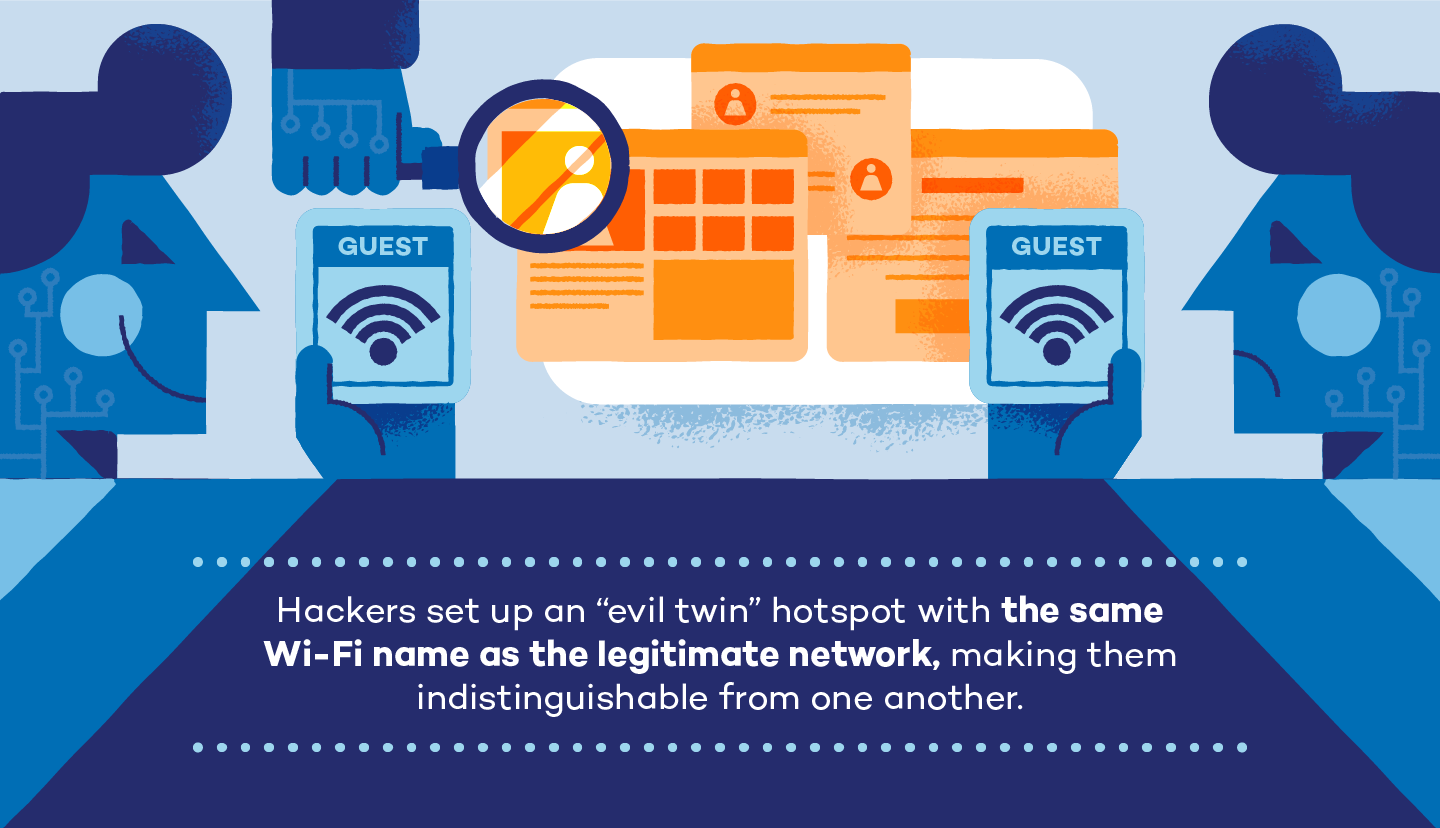
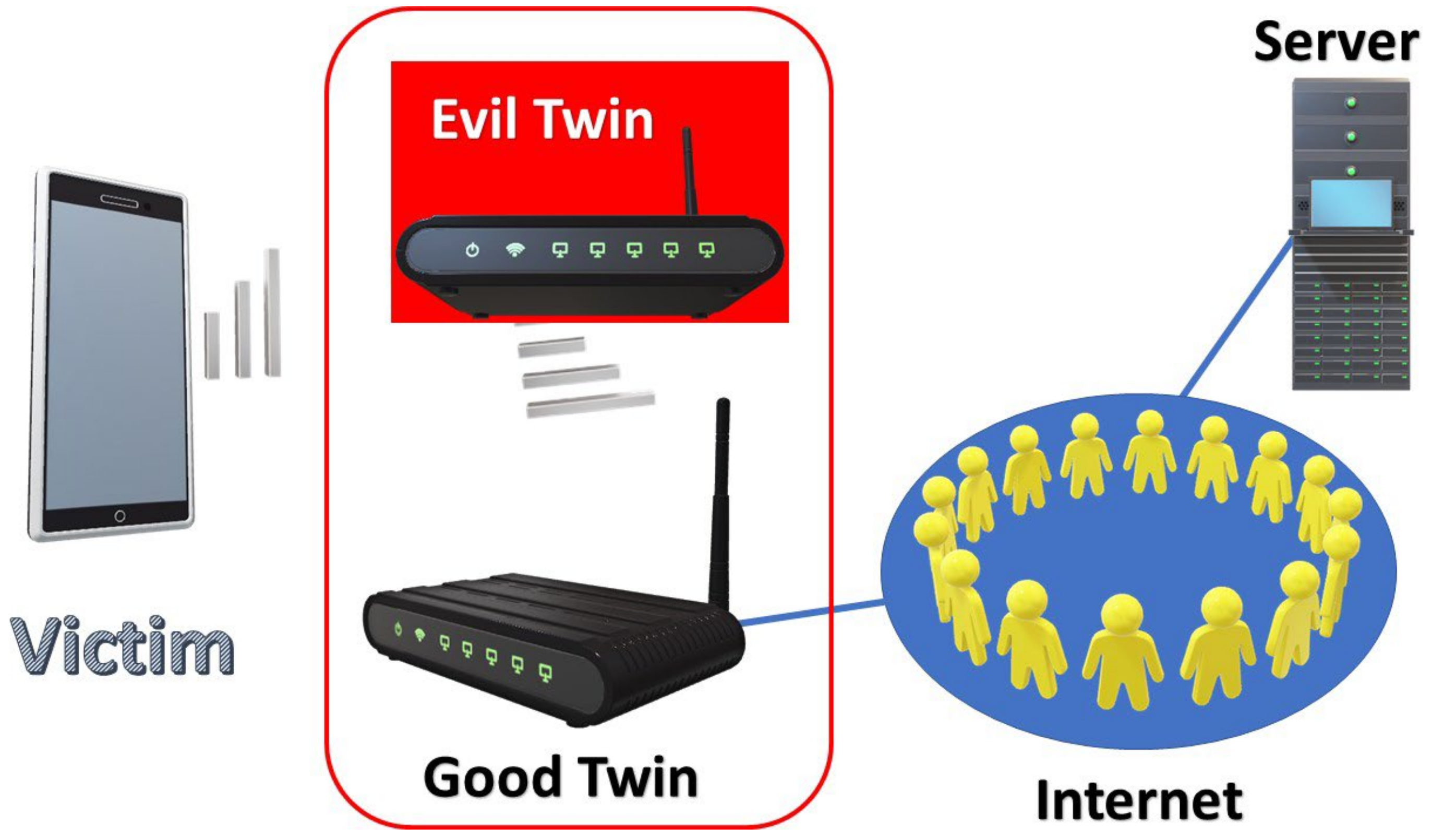
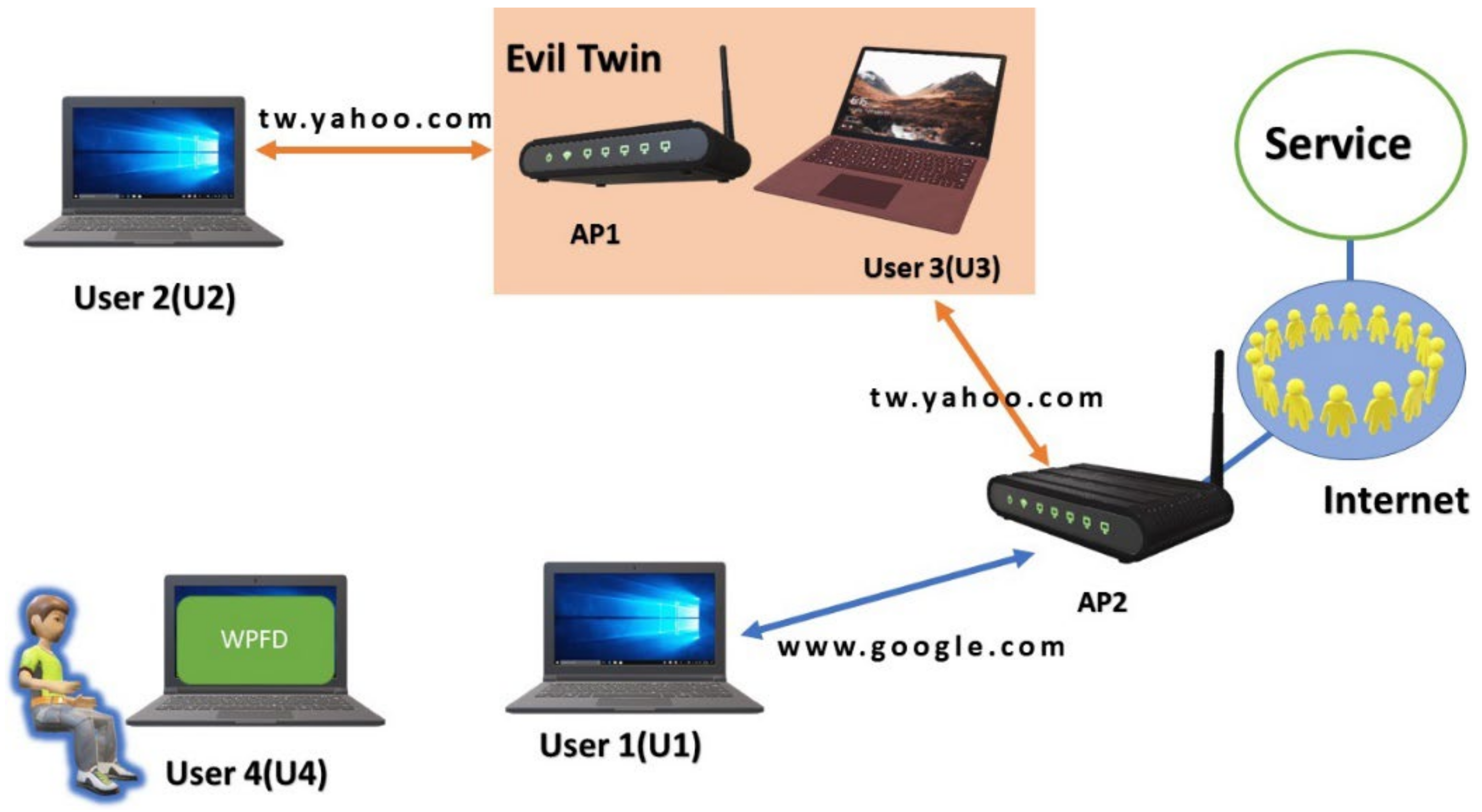
An Efficient Scheme to Detect Evil Twin Rogue Access Point Attack in 802.11 Wi-Fi Networks | SpringerLink

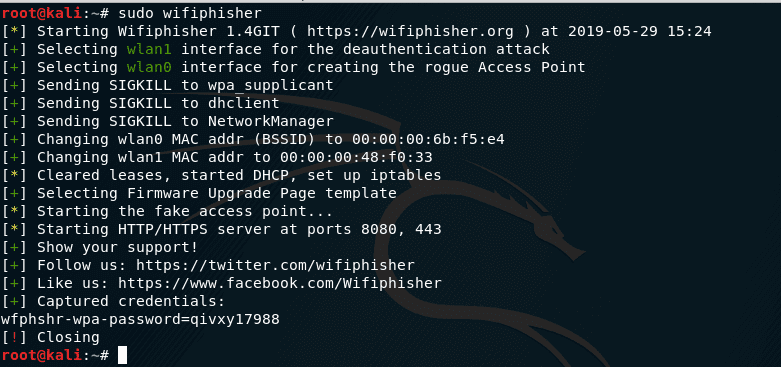
Ethical Hacking wifi hacking | Evil-Twin Attack Part 18 of Ethical Hacking??? #ethicalpakistan #hackingpakistan #blackhathacking #ethicalacademy #Eviltwinattack #fluxion... | By Ethical And Black Hat Academy | Facebook